When it comes to safeguarding online activities, the phrase “VPN with no logs and strong encryption” has become a benchmark for privacy‑conscious users. In an era where data breaches and surveillance are commonplace, a virtual private network that promises both zero‑log policies and robust cryptography offers a reliable shield against prying eyes. This article walks you through the technical foundations, practical implications, and selection criteria for such VPN services, helping you make an informed decision without wading through marketing hype.
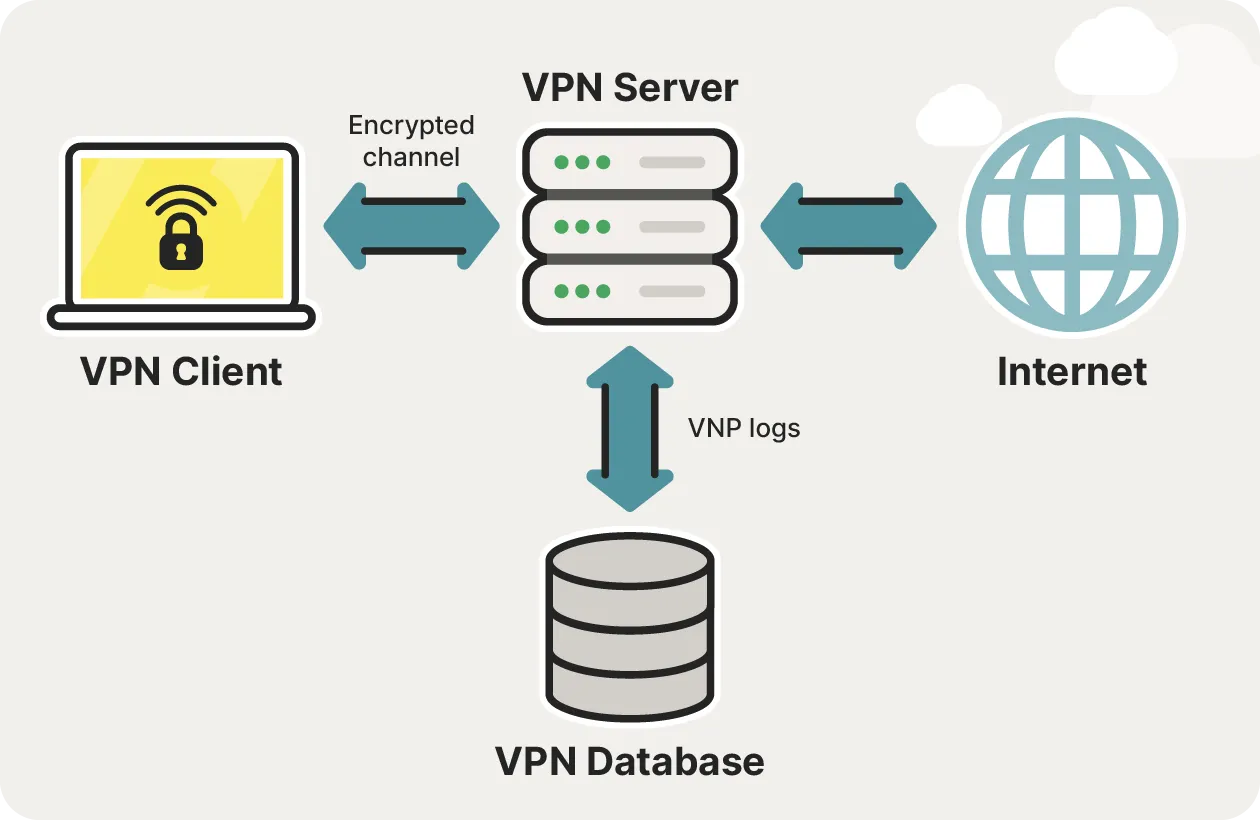
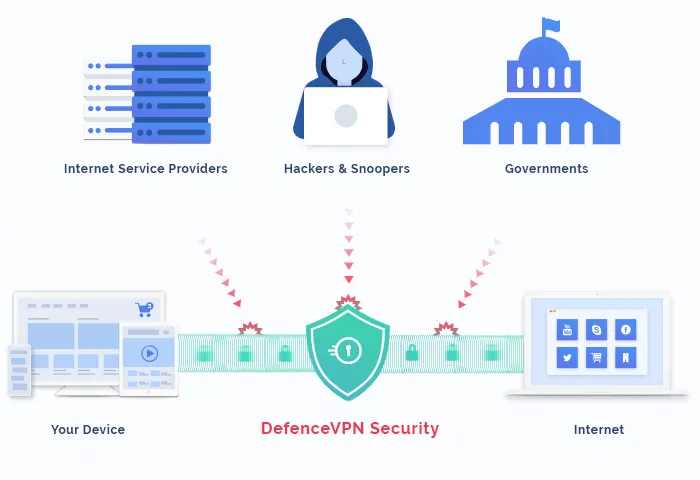
Understanding why “no‑log” and “strong encryption” matter is the first step toward building a secure digital routine. A no‑log VPN ensures that the provider does not retain any record of your traffic, IP address, or connection timestamps, effectively removing the data trail that could be handed over to authorities or sold to advertisers. Strong encryption, on the other hand, scrambles the data packets that travel between your device and the VPN server, making it virtually unreadable to anyone who might intercept them. Together, these two pillars form a robust privacy architecture that can protect everything from personal emails to corporate transactions.
Below, we explore how these concepts translate into real‑world technology, what you should verify before subscribing, and how a well‑chosen VPN can integrate seamlessly into daily activities—whether you’re streaming, gaming, or running a small business.
What Defines a “No‑Log” VPN?
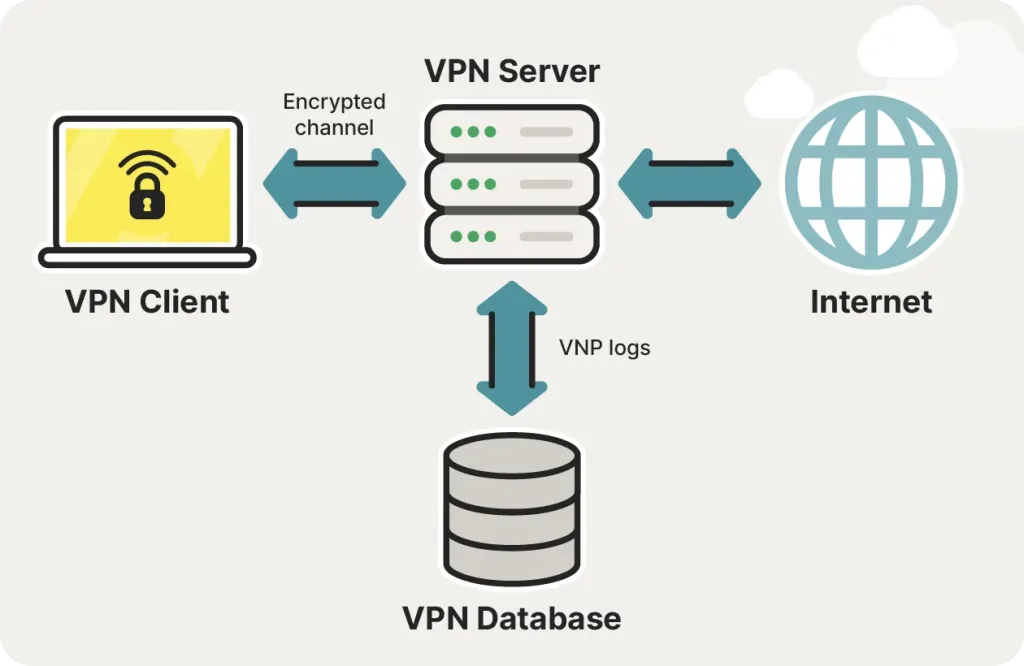
The term “no‑log” might sound straightforward, but the reality involves several layers of policy, technical design, and legal jurisdiction. A truly no‑log VPN commits to not storing any metadata that could be linked back to a user.
Understanding Log Policies
- Connection logs: Records of timestamps, duration, and IP addresses. A no‑log service does not keep these.
- Traffic logs: Details about the websites you visit or data you transmit. These must be absent in a privacy‑first VPN.
- Bandwidth usage: Some providers log total data transferred for network management. The strictest no‑log policies omit even this.
Technical Measures to Enforce No‑Logging
- RAM‑only servers that lose all data on reboot.
- Automated log‑purge scripts that erase any temporary records within minutes.
- Independent audits performed by third‑party security firms, often resulting in publicly available audit reports.
Legal Considerations
The jurisdiction where a VPN is headquartered dictates the legal obligations to retain or disclose user data. Countries with strong privacy laws (e.g., Switzerland, Panama, the British Virgin Islands) are preferred because they lack mandatory data‑retention statutes. Conversely, providers based in the Five‑Eyes alliance (USA, UK, Canada, Australia, New Zealand) may be compelled to hand over any logs, however minimal.
How Strong Encryption Works in VPNs
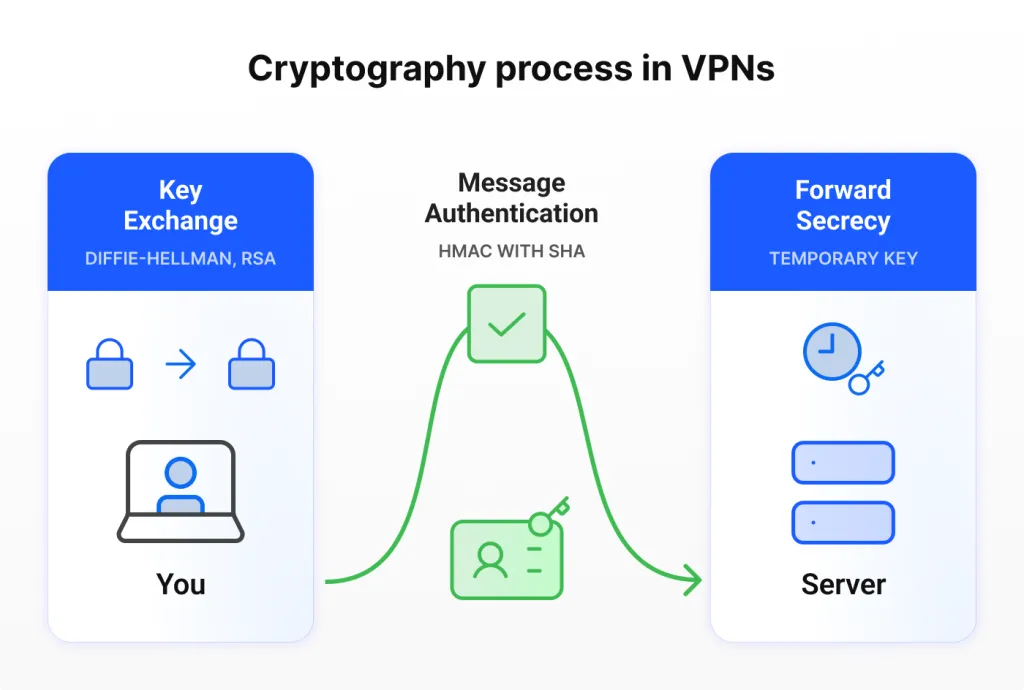
Encryption is the process of converting readable data into an unreadable format using mathematical algorithms. In VPNs, two primary components work together: the encryption algorithm (cipher) and the key exchange protocol.
Encryption Algorithms (Ciphers)
- AES‑256‑GCM: The gold standard for symmetric encryption, offering 256‑bit keys and authenticated encryption for integrity.
- ChaCha20‑Poly1305: A modern alternative that provides comparable security with better performance on mobile CPUs.
- Legacy ciphers (e.g., DES, 3DES): Should be avoided as they are vulnerable to modern cryptanalysis.
Key Exchange Protocols
- OpenVPN (TLS 1.2/1.3): Uses the Diffie‑Hellman or Elliptic Curve Diffie‑Hellman (ECDH) methods to securely negotiate keys.
- WireGuard: Relies on the Noise protocol framework, offering streamlined key exchange and reduced attack surface.
- IKEv2/IPsec: Popular for mobile devices due to its resilience to network changes, also supports strong ciphers like AES‑256.
Perfect Forward Secrecy (PFS)
PFS ensures that even if a private key is compromised in the future, past sessions remain secure because each session generates a unique temporary key. Look for VPNs that explicitly state support for PFS.
Choosing a VPN That Combines No‑Logs and Strong Encryption
Selecting the right provider involves a checklist that balances policy, technology, and user experience. Below is a practical framework you can apply.
Checklist for Evaluating Providers
- Transparent No‑Log Policy: Written in plain language, no vague clauses.
- Independent Audit: Look for recent third‑party audit results (e.g., PwC, Deloitte).
- Jurisdiction: Prefer privacy‑friendly locations.
- Encryption Suite: Must support AES‑256‑GCM or ChaCha20‑Poly1305 with PFS.
- Protocol Options: Availability of OpenVPN, WireGuard, and IKEv2.
- Kill Switch: Guarantees traffic stops if the VPN tunnel drops.
- DNS Leak Protection: Prevents accidental exposure of DNS queries.
- Performance: Low latency and sufficient bandwidth for your primary use case.
Real‑World Use Cases
If you’re a gamer, you’ll want a VPN that not only respects privacy but also maintains low ping. Discover the Fastest VPN for Gaming and Low Ping – Boost Your Win Rate Today provides a detailed comparison of speed‑focused services that also uphold strict no‑log standards.
Small business owners often balance budget constraints with security needs. A guide such as How to Choose an Affordable VPN for Small Businesses Without Compromising Security outlines cost‑effective options that still deliver strong encryption and zero‑log policies.
Performance Implications of Strong Encryption
Strong encryption can introduce a marginal overhead, typically ranging from 2% to 10% depending on the cipher, hardware, and network conditions. Modern CPUs with built‑in AES‑NI (AES New Instructions) mitigate this impact, making AES‑256‑GCM practically indistinguishable from unencrypted traffic in everyday use.
Optimizing Speed Without Sacrificing Security
- Choose a server geographically close to you.
- Prefer WireGuard if your device supports it; its lightweight design reduces latency.
- Enable split tunneling to route only sensitive traffic through the VPN.
- Use a VPN provider that employs SSD‑backed servers for faster handshake and data processing.
Potential Pitfalls and How to Avoid Them
Even with a no‑log policy and strong encryption, users can unintentionally compromise privacy through misconfiguration or poor habits.
Common Mistakes
- Using Free VPNs: They often monetize through data collection, directly contradicting a no‑log promise.
- Disabling Kill Switch: Leaves a brief window where traffic leaks if the connection drops.
- Relying on Default DNS: Your ISP’s DNS can reveal the sites you visit, bypassing the VPN’s protection.
- Ignoring Software Updates: Outdated clients may have vulnerabilities that attackers can exploit.
Best Practices
- Regularly audit your VPN settings (kill switch, DNS leak protection).
- Combine VPN use with secure browsers that block trackers.
- Consider a multi‑hop VPN configuration for added anonymity, especially when dealing with high‑risk activities.
The Future of No‑Log, Strong‑Encryption VPNs
As regulatory environments evolve and quantum computing threatens conventional cryptography, VPN providers are already researching post‑quantum algorithms and decentralized architectures. Decentralized VPNs (dVPNs) built on blockchain technology aim to distribute trust among many nodes, reducing reliance on a single corporate entity that could be compelled to keep logs. While still early in adoption, these innovations suggest that the privacy landscape will continue to strengthen.
Meanwhile, the core principles of zero logging and strong encryption remain the foundation of trustworthy VPN services. By staying informed about policy changes, technical upgrades, and emerging threats, users can ensure that their digital footprints stay hidden, no matter how sophisticated the surveillance tools become.
Choosing a VPN that genuinely respects your privacy is not a one‑time purchase; it’s an ongoing partnership between you and a service provider committed to transparency, security, and performance. Armed with the knowledge from this guide, you can evaluate options critically, avoid common pitfalls, and enjoy the internet with confidence.